Work From Home 2020 Malwares has flooded the cyberworld. Companies were ready and are getting ready with the traditional defenses such as VPN, updated Antivirus, Multi-Factor Authentication and other basics checklist on awareness and compliance. CyberCrooks are targeting Advanced Attacks on End Points by Embedding malware in documents, web-links, applications and executing file-less and in-memory attacks which is the big worry for CIO's and CISO.
Infopercept�Antidote for WFH2020 Malwares whitelists your worries, whereby our unique approach with the combination of Morphing Application and Moving Target Defence Concept at the endpoint fights attackers at endpoint for advance attacks and still not leaving a chance of compromise Infopercept performs the same strategy of Physical world in Digital World where we create an isolated environment and conduct compromise assessment for all user coming from the vulnerable foreign network before allowing them in the business network.
We create a complete landscape to proactively monitor and protect advanced attacks as Individuals foresee the Year 2020 as a leap to Cyber Crimes.
The lack of IT resources can worry about many companies as they move to enable remote strategies. And when the majority of employees are operating outside the company perimeter, managing device sprawl, and patching and securing many endpoints
It becomes a much bigger challenge for the CEOs and CIOs. According to the Global Threat Index of a leading security solutions provider, cyber-criminals are exploiting the global epidemic by spreading malicious activity and launching spam campaigns relating to the outbreak of the virus.
Are Honeypots the same as for Deception Platforms?
The Deception Era

Deception, the Preferred Method for Detection
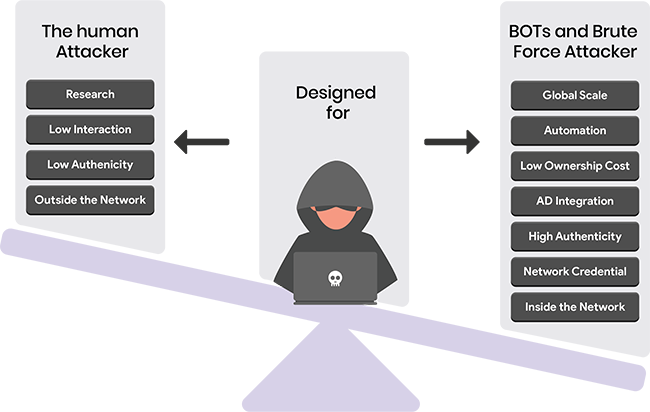
Efficient, Scalable, In-Network Threat Detection that changes the asymmetry of an attack.
It is could be defined as the concept of controlling change across multiple system dimensions in order to increase uncertainty and apparent complexity for attackers, reduce their window of opportunity and increase the costs of their probing and attack efforts.
The never-ending competition between cyber attackers and cyber defenders has gained unprecedented levels of sophistication and complication. As defenders adopt new detection and response tools, attackers develop various techniques and methods to bypass those mechanisms. And deception is one of the most effective weapons on both sides of the game.
Infopercept believes that Deception techniques have traditionally been among the favorite methods in the attacker's arsenal. Surprise and uncertainty provide the attackers with an inherent advantage over the defender, who cannot predict the attacker's next move.
Moving Target Defense (MTD) aims at creating asymmetric uncertainty on the attacker's side, by changing the attack surface.
This point of view comes from the understanding that absolute security is not an achievable goal; there is an asymmetry between the attackers and the defender's costs and efforts. Therefore, there is a need to implement a new paradigm for changing the costs and efforts in this adversarial game.
Watch our video:�https://youtu.be/9t7vgbVVXWA








Do you fear that we might not do the task as you asked us to? Don�t worry � we even have free revisions, and unlimited ones, to cover any situation where you�re unhappy with your paper. Quality here is guaranteed and proven, over and over again for��to complete the project. Your assignment worries are now released here, just when you say, "write my assignment for me". We deal with variety of subjects and assignment types. Contact us whether it is your biology assignment, chemistry, IT, Law, management marketing, nursing or business studies; we work on all under one umbrella. Our team knows about all the basics, as we offer:�custom assignment writing service UK. One of the outcomes is that you procrastinate and complete the paper the same day it is due. In this visualisation, you can observe yourself in a panicked stated, where you are just rushing to add words on the�. As a result, you compromise the quality of the work, and the grade you receive is low. In such situations, you can apply the ten-minute rule, which states that you can endure any difficult situation for just ten minutes. By thinking this, you can continue writing your project for ten minutes. However, when the ten-minute time frame is completed, you can spend another ten minutes on the project as you realise your potential to work continuously for ten minutes. This cycle can be repeated until your project is completed. Sometimes you do not want to attempt the academic project because it is too overwhelming to look at�custom dissertation writing service UK. Even if you persuade yourself to do it, looking at the amount of work that needs to be done reduces your motivation to attempt the project. In this case, you can invest some time in breaking the task down and creating a schedule to complete each component of the project. One of the motivating factors for any human being is getting a reward after�custom essay writing service UK. Keeping this in mind, you can offer yourself a reward for completing the project. The reward you offer must hold value to you. For example, you can watch your favourite movies after completing the essay, or you can have your favourite ice-cream.
�